This is an old revision of the document!
- slackware
- Jonathan Haack
- Haack's Networking
- netcmnd@jonathanhaack.com
Install os, then add non-root user:
adduser
Follow the prompts then join wheel group, then add these by using up arrow
wheel,floppy,audio,video,cdrom,plugdev,power,netdev,lp,scanner
Set up WPA2 network:
nano /etc/wpa_supplicant.conf
Make it look like this:
ctrl_interface=/var/run/wpa_supplicant
ctrl_interface_group=0
eapol_version=1
ap_scan=1
fast_reauth=1
network={
scan_ssid=0
ssid="your_essid"
proto=WPA2
key_mgmt=WPA-PSK WPA-EAP
pairwise=CCMP TKIP
group=CCMP TKIP
psk=your_64_hex_characters_long_key
}
To get your psk key, run:
wpa_passphrase ssid 'passphrase'
Then, edit the /etc/rc.d/rc.inet1.conf as follows:
IFNAME[1]="ath0" IPADDR[1]="" NETMASK[1]="" USE_DHCP[1]="yes" DHCP_HOSTNAME[1]="" [leave blank if using more than one SSID, and let wpa_supplicant priority handle] WLAN_WPA[1]="wpa_supplicant" WLAN_WPADRIVER[1]="wext"
Once everything is configured, restart the interface as follows - if everything connects, and you get the nickname error, just ignore it as it will go away on reboot:
/etc/rc.d/rc.inet1 wlan0_restart
Okay, now to add open networks, just add the following to wpa_supplicant:
network={
ssid="sitc"
key_mgmt=NONE
}
Later, I will add how one can use priority = within these configs to cycle through various networks in a specific order, but for now, it is easiest to switch manually as follows:
iwconfig wlan0 essid <nameofssid>
Now that you are online, let's set up sudoer access:
nano /etc/sudoers
Then, add this directly below the root user line that is similar to this:
username ALL=(ALL) ALL
Now, how to update packages:
nano /etc/slackpkg/mirrors
Uncomment one of the mirrors from USA - use http - once that is done:
slackpkg update gpg slackpkg update slackpkg install-new slackpkg upgrade-all slackpkg clean-system
Set up a crypt for sensitive data:
cryptsetup luksFormat /dev/sdaX cryptsetup luksOpen /dev/sdaX vault mkfs.xfs -L vault /dev/mapper/vault mkdir /mnt/vault mount /dev/mapper/vault /mnt/vault
After you reboot and login again, then open the crypt and mount it as follows:
cryptsetup luksOpen /dev/sdaX vault <enter passphrase> mount /dev/mapper/vault /mnt/vault
Okay, this is method 2, encrypting the whole system except for the boot partition using Grey Seeker tutorial. First, lets create our partitions using gdisk:
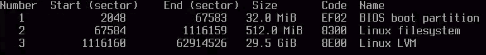
gdisk /dev/sda <n, enter, enter, +512M, ef02 code for BIOS boot> <n, enter, enter, +2000M, default code for /boot partition> <n, enter, enter, enter, 8e00 code for LVM> <p, to print the configuration of the partitions>
If you did that correctly, it will look like this:
If everything looks good, then execute the following in gdisk:
<w, Y, enter>
Now, it is time to configure LVM:
cryptsetup luksFormat -c aes-xts-plain64:sha512 -h sha512 -s 256 /dev/sda3 cryptsetup luksOpen /dev/sda3 vault0
Now, it is time to create the physical volume, and then after that, the logical volume group, then the logical volumes:
pvcreate /dev/mapper/vault0 vgcreate slack /dev/mapper/vault0 lvcreate -C y -L 8G -n swap slack lvcreate -C n -L 32G -n root slack lvcreate -C n -l 100%FREE -n home slack
— oemb1905 2019/06/13 09:38